JNDI Injection — The Complete Story ⌘ Read more
Hundreds of companies’ internal data exposed — Part 2: The FreshService misconfiguration ⌘ Read more
HacktheBox Starting Point: Explosion Walkthrough ⌘ Read more
5 Ways I Can Find Your Deleted Files as An Ethical Hacker! ⌘ Read more
For Business Reasons | TryHackMe Write-Up ⌘ Read more
BSQL Injection Shenanigans ⌘ Read more
Bypassing UAC ⌘ Read more
My LLM Bug Bounty Journey on Hugging Face Hub via Protect AI
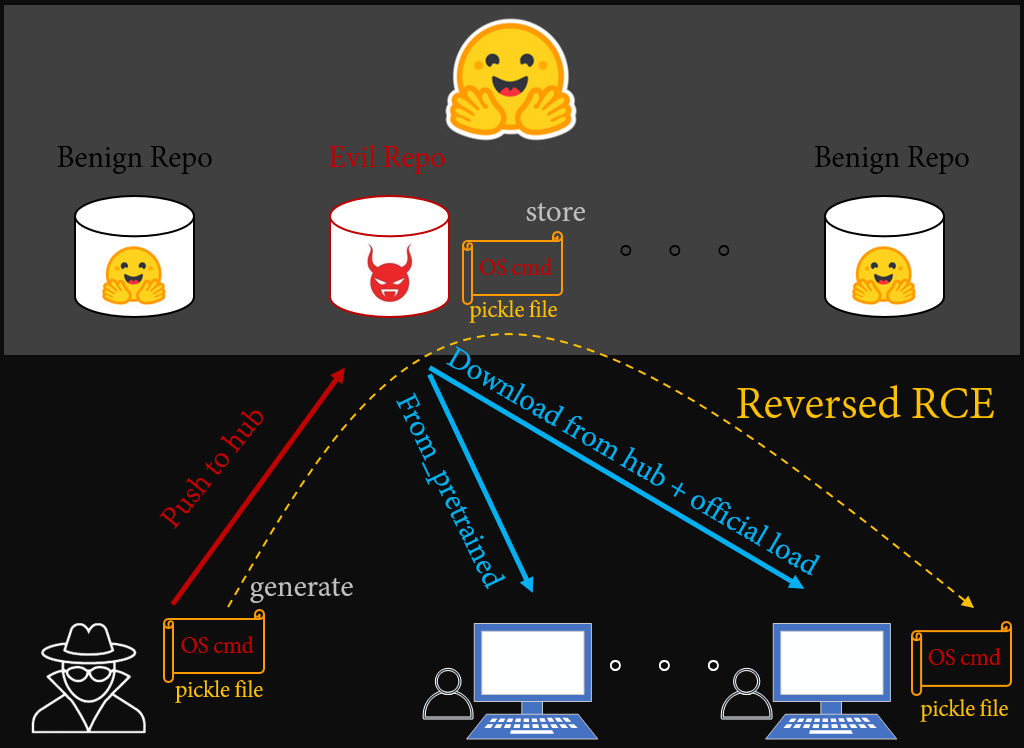
From Informative Rejection to Black Hat Briefing
[Continue reading on InfoSec Write-ups »](https://infosecwriteups.com/my-llm-bug-bounty-journey-on-hugging-face-hub-v … ⌘ Read more
Hacking into 30+ tesla cars around the world using a third party software ⌘ Read more
Creative | TryHackMe Write-Up ⌘ Read more
Hook, Line, and Sinker: Navigating the Waters of Phishing Attacks in 2024 ⌘ Read more
My Hunt: Discovering Microsoft Bugs
Navigating the Terrain of Microsoft’s Software: Insights from a Bug Hunter
A Guide To Securing Your Remote Access Using SSH Keys ⌘ Read more
WolvCTF 2024: Forensics Challenges ⌘ Read more
Cyber-attacks, malware, and aspects of ransomware.
Hacking Web Meeting/Webinar App ⌘ Read more
Privilege Escalation Using SCIM Provisioning ⌘ Read more
Admin Account Takeover ⌘ Read more
Sensitive data leak using IDOR in integration service ⌘ Read more
Understanding Zero Trust Architecture: A New Paradigm in Cybersecurity ⌘ Read more
HackTheBox Academy: Privilege Escalation ⌘ Read more
Incident Response: A Comprehensive Guide for Businesses and Cybersecurity Professionals ⌘ Read more
Unlocking ChatGPT’s Internal Prompts: A Guide to Reverse Engineering AI Conversation Models

Discover how to reverse engineer ChatGPT’s internal prompts, unraveling the st … ⌘ Read more
AWS S3 Bucket Misconfiguration Exposes PII and Documents of Job Seekers ⌘ Read more

